.jpg)
Transcript
A Guide to AI-Powered Network Security Workflows
Network security teams in 2025 live in a state of permanent triage.
The work never shows up one task at a time, it arrives as in a queue: noisy logs, creeping exposures, incident follow-ups, and configuration drift that all compete for attention. Manual handling across these workflows is slow, inconsistent, and easy to get wrong at scale.
AI powered automation (like Kindo’s agents) changes that by analyzing data and enforcing standards continuously in the background. The payoff is simple: fewer tedious checks, faster decisions, and more time focused on real threats. In this post, we’ll walk through five network security workflows that AI can optimize.
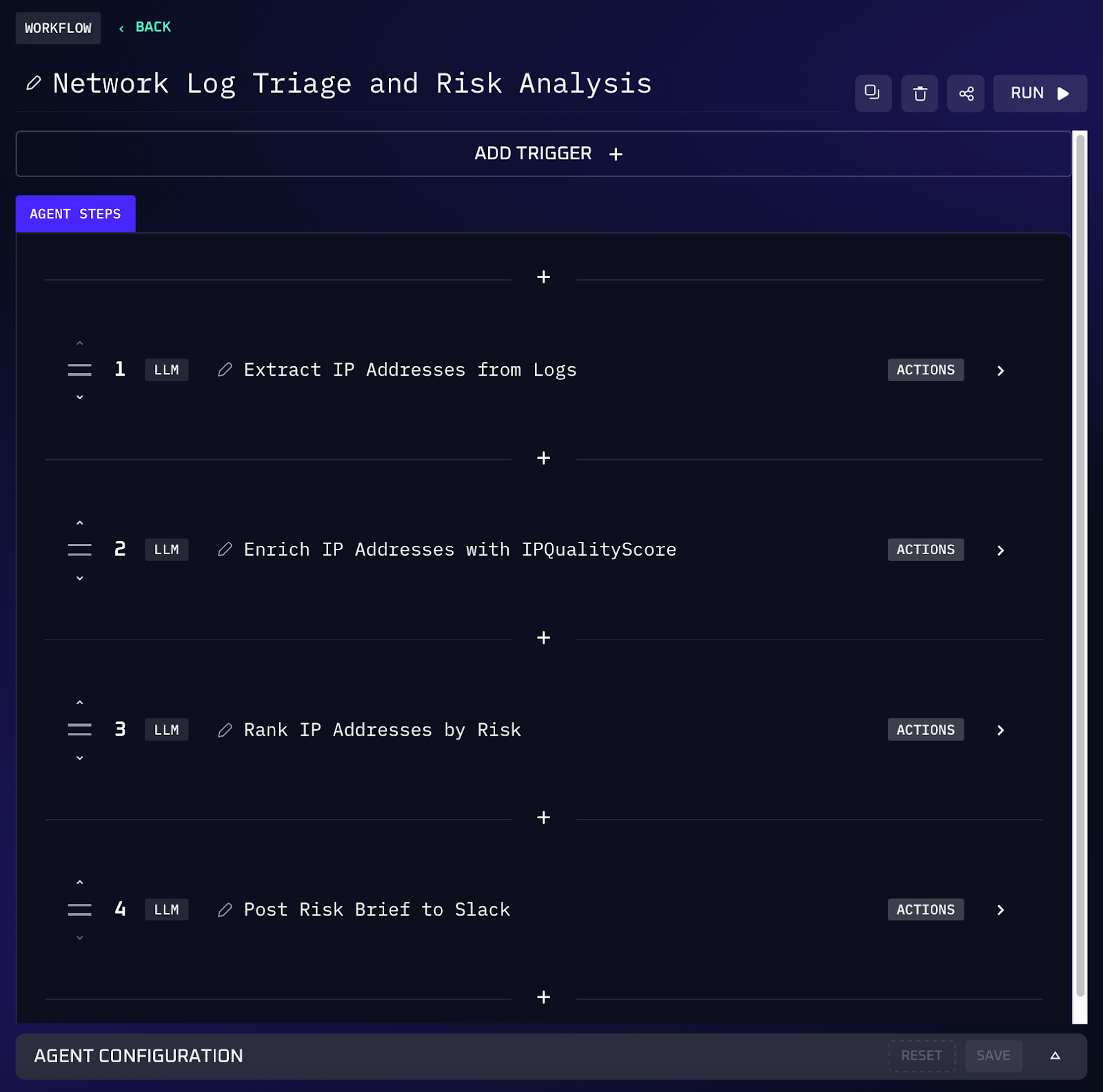
1. IP Reputation Triage from Network Telemetry
When monitoring network logs, analysts often encounter dozens or hundreds of IP addresses hitting their systems. Determining which of those IPs are malicious versus benign can involve a lot of tedious lookups. Traditionally, an analyst might pivot to multiple websites or tools for each suspicious IP: checking reputation on threat intel services, querying WHOIS for ownership, searching blacklists, etc. This is slow work and it’s easy to overlook indicators in a sea of addresses.
This workflow automates IP reputation triage directly from raw network telemetry. You simply provide the logs, and the AI agent extracts all unique IP addresses observed. The agent then uses an IP reputation service (like IPQualityScore) to retrieve threat scores for each IP. It compiles a ranked list of the IPs by risk level (and by how frequently they appear), so the worst offenders stand out.
Workflow Steps (IP Extraction & Risk Scoring)
1. The AI agent ingests the uploaded network log and parses it to find all unique IP addresses that appear (as source or destination).
2. For each IP, the agent queries a reputation database or API (for example, the IPQualityScore API) to fetch a threat score and any contextual data (e.g. malicious, suspicious, or clean).
3. The agent compiles the results into a list of IP addresses with their threat scores and notable details. It also notes how many times each IP appears in the log, because a frequently seen high risk IP could indicate active targeting.
4. Using the collected data, the agent ranks the IP addresses from highest risk to lowest. Any IP above a defined risk threshold is flagged for immediate attention.
5. The workflow produces a summary of the findings. This summary is then posted to the designated Slack channel, alerting the team in near real time.
Value of Automation
Automating IP log triage means analysts get instant insight without the manual drudgery. Instead of individually pasting IPs into various lookup tools, the enrichment workflow delivers a one-stop report. This dramatically cuts down analysis time when reviewing firewall or IDS logs. Equally important, the process is thorough and consistent, every IP is checked against the same intelligence source, ensuring no suspicious address goes unchecked.
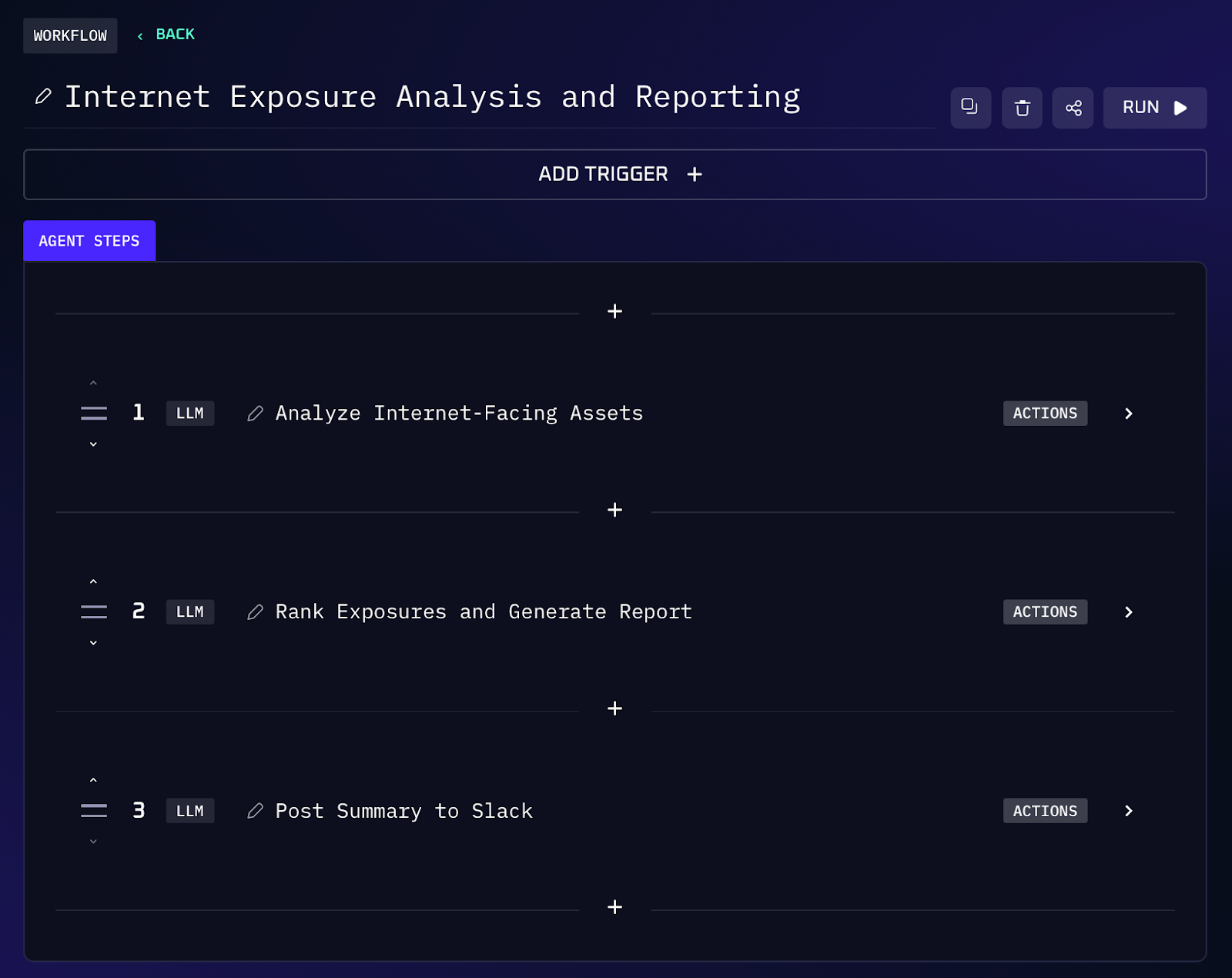
2. Internet-Facing Service Exposure Map
Keeping track of what services your organization is exposing to the internet is a never ending task. Servers and cloud resources can inadvertently have ports open or services reachable from the outside, introducing risk. Traditionally, security teams compiled data from external scanners like Shodan or Censys (or run their own Nmap sweeps) and then manually sifted through the results to identify the most dangerous exposures.
This AI workflow consolidates all that attack surface data and automatically shows the worst risks. You might start with an input like a list of internet-facing assets or a recent scan export. The agent parses the inventory and flags obvious issues. It cross-references service versions with known vulnerabilities, so if a server is running a version with a critical CVE, that gets elevated in priority. The output is a clear list of exposures (each annotated with why it’s risky), along with an executive summary of the overall external risk posture.
Workflow Steps (Exposure Analysis & Ranking)
1. The workflow takes an input inventory of assets and services. This could be an export from external scanners (like Shodan/Censys data, cloud asset lists) or results from an Nmap scan of the organization’s IP ranges.
2. The agent parses the data to identify all publicly exposed services. It notes each host or IP, the open ports, the service running on those ports, and any available version information or banners.
3. Next, the agent evaluates each exposed service against a set of risk criteria. It flags common high risk scenarios.
4. If version information is available, the agent cross-references each service against known vulnerability databases. As an example, a service running an outdated version with critical CVEs is marked as the highest risk.
5. The agent then prioritizes the most concerning exposures. Alongside this list, the workflow generates an executive summary showing the overall exposure level. This summary and the detailed fix list are then sent via Slack to ensure immediate visibility.
Value of Automation
By aggregating disparate scan data into one workflow, this process provides an up to date snapshot of your attack surface without manual collation. Security teams no longer have to comb through spreadsheets or lengthy scan reports, the AI automatically pinpoints exposures. This ensures that nothing slips through the cracks. The prioritized output also helps teams remediate intelligently. Instead of guessing which issues to tackle first, the worst problems are shown with clear rationale. Teams can immediately focus on closing the most dangerous gaps, reducing the window of exposure.
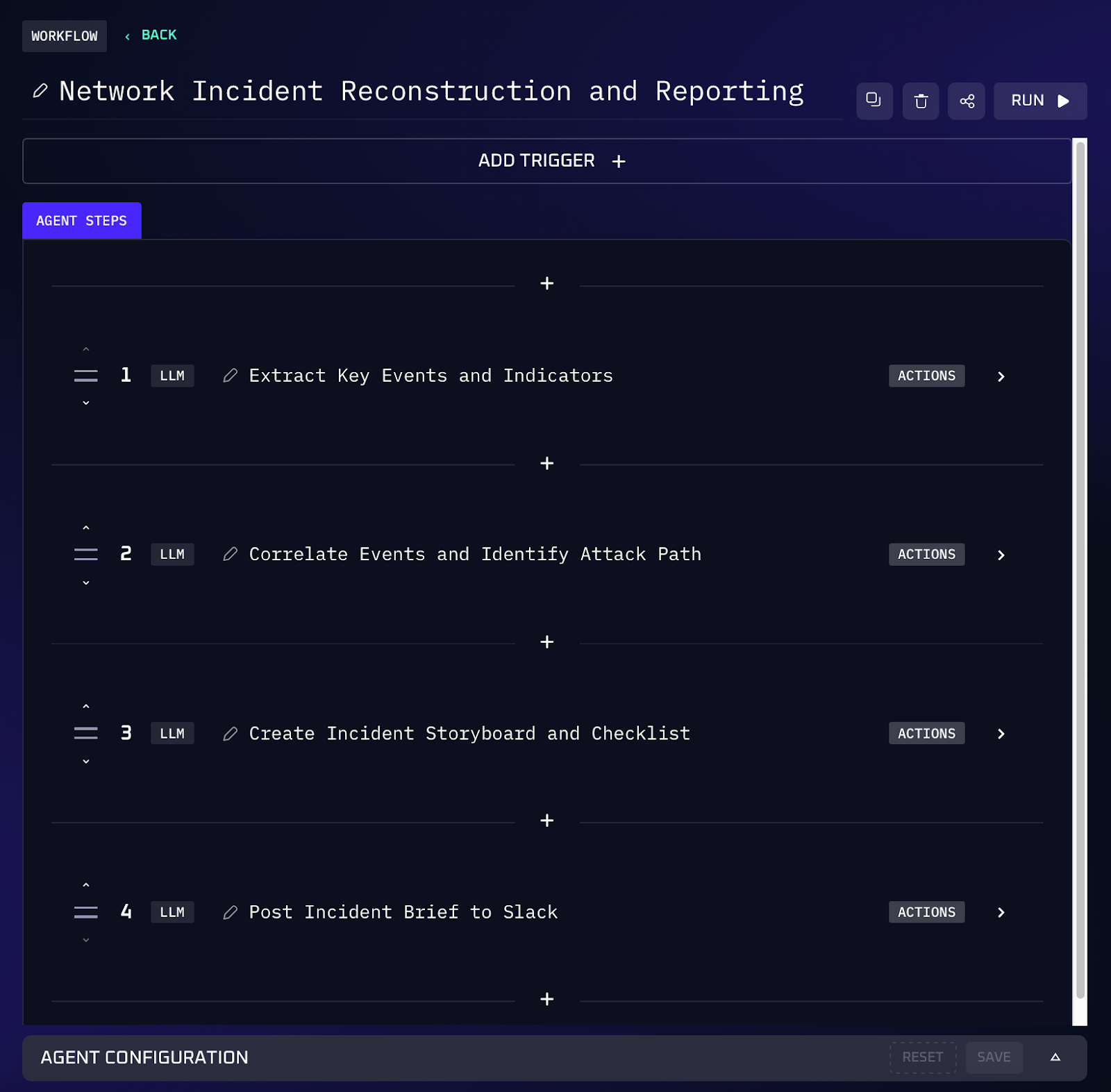
3. Network Incident Timeline Reconstruction
Handling a network security incident often means piecing together evidence from many sources. A single incident ticket might have IDS alerts, packet capture (PCAP) files, malware sandbox reports, and notes from multiple analysts. Manually correlating all this into a coherent timeline is painstaking work. Investigators must pull key clues from each artifact (timestamps, IP addresses, malware behavior) and reconstruct the attacker’s steps. It’s easy to miss connections or spend hours writing up the incident narrative when you’re already under pressure to respond.
This workflow turns that pile of incident evidence into a clear, actionable story automatically. You feed the AI agent the incident ticket details and all attachments, and it does the heavy lifting. The agent parses everything, pulling out key events from the PCAP (like suspicious connections), reading the IDS/alert messages, extracting malware behavior from the sandbox report, and piecing them together chronologically. The result is an incident storyboard describing the intrusion flow. It also provides the top three hypotheses for the attacker’s objectives or methods.
Workflow Steps (Incident Analysis & Storyboarding)
1. The analyst provides the AI agent with the incident ticket details and all related evidence files (logs, PCAPs, malware reports, screenshots, notes, etc.).
2. The agent parses each artifact for key information. It extracts relevant events and indicators: network connections and timestamps from PCAPs, alert descriptions and fields from log files, and observables from malware reports.
3. The agent correlates these findings by timestamp to build a chronological timeline of the incident. Events from different sources are merged into a single sequence, allowing it to identify phases like initial compromise, lateral movement, privilege escalation, and data exfiltration if they occurred.
4. Based on the timeline and indicators, the agent identifies likely attack paths and methods. It determines the probable initial access vector and how the attacker moved through the network. It also formulates the top 3 hypotheses about the attack’s nature or goal.
5. The workflow outputs a comprehensive incident storyboard. This includes a narrative of what happened and a recommended next-step checklist. An alert is posted to Slack to ensure the team is immediately informed of the findings.
Value of Automation
This automation can save incident responders hours. Instead of spending half a day pulling threads from various logs and evidence files, the AI delivers a consolidated narrative in minutes. It ensures no important detail is overlooked in the chaos of an incident, and every relevant indicator is accounted for. Another benefit is consistency, each incident is documented in a standardized format, regardless of who the analyst is. The structured storyboard shows the main events and suspects right away, allowing the team to respond faster and with greater confidence. Less experienced team members can also handle complex incidents with the AI’s assistance, because the heavy lifting of analysis is done for them.
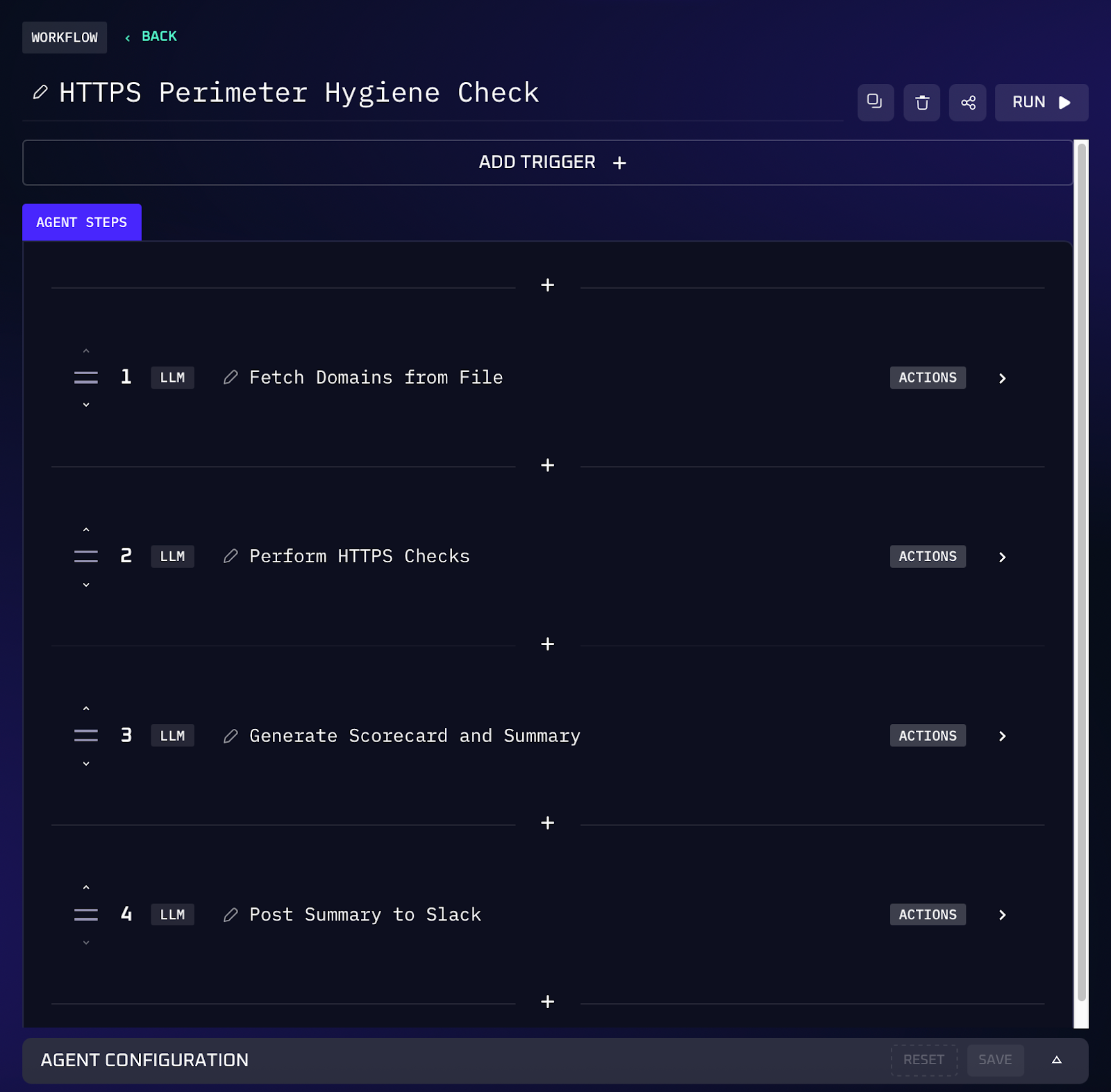
4. Continuous TLS/HTTPS Perimeter Hygiene Scoring
Maintaining strong web security at the edge, specifically, ensuring all your public websites enforce HTTPS protections, is important for defending against web-based attacks. Many organizations have numerous external domains and web applications, and checking that each one has the proper security headers (for HSTS, content security, clickjacking, etc.) can be a challenge.
This workflow provides a continuous scorecard of your domains’ HTTPS security posture by directly analyzing their response headers. You supply a list of domain names, and the AI agent checks each one in turn. Each domain is then given a clear score out of 100 based on a simple baseline weighting these controls. The agent compiles a report showing each domain’s score and which headers are missing or weak for those that didn’t meet the standard.
Workflow Steps (Header Audit & Scoring)
1. The workflow starts with an input list of domains or hostnames that need their HTTPS configurations evaluated.
2. For each domain, the AI agent makes an HTTPS request (typically a HEAD request) to fetch the site’s response headers.
3. The agent examines the headers returned, checking for the presence and correctness of security headers.
4. The agent calculates a security score for each domain based on these headers. For example, a site with all the above headers correctly set might score 100, whereas a site missing HSTS or several others will score lower (the scoring rubric is a lightweight baseline giving more weight to key headers like HSTS).
5. The workflow flags any domain that falls below the acceptable threshold or is missing important controls. The agent outputs the full scorecard for all domains and posts a Slack alert summarizing the results.
Value of Automation
This automated scorecard provides a simple but effective gauge of your organization’s web security hygiene. By regularly checking these headers across all your sites, the team can catch misconfigurations or omissions early, long before an external auditor or attacker does. It’s a lightweight process (just reading HTTP headers) with high impact results: a missing HSTS or CSP header might seem minor, but those omissions can dramatically increase risk of man-in-the-middle or cross-site scripting attacks. Automation ensures these checks happen continuously and consistently, so even a small oversight gets flagged and fixed promptly.
5. Network Segmentation Policy Integrity Checks
Network segmentation policies rarely stay aligned with the intended security model for long. Firewall rules, cloud security groups, SD-WAN rules, micro-segmentation policies, and VLAN boundaries are constantly updated as new applications roll out, environments change, and urgent access exceptions are introduced. Over time, segmentation controls can become inconsistent with the approved design: restricted zones may gain new pathways, broad rules may replace narrow ones, and temporary exceptions may persist without review.
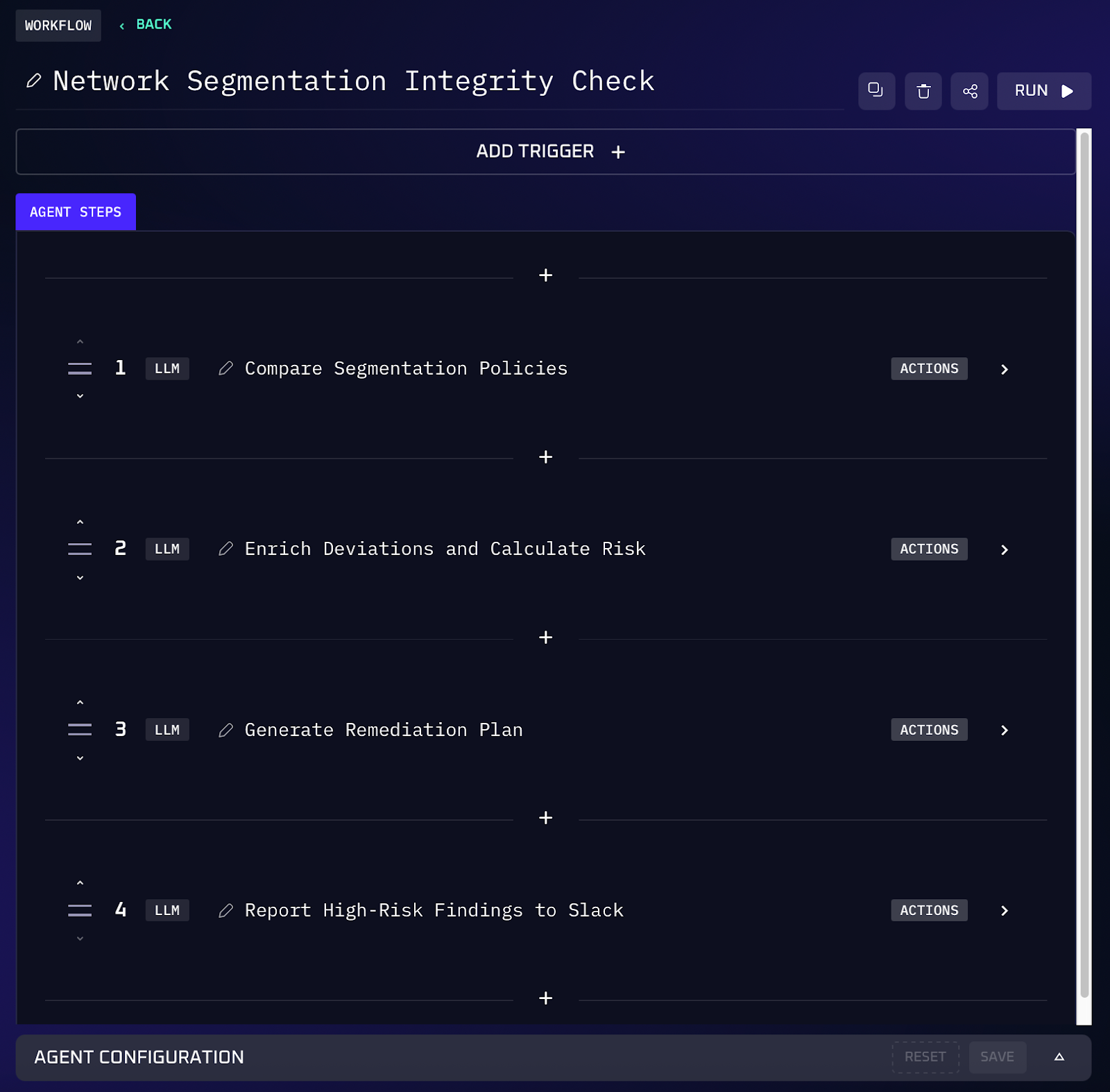
This workflow automates segmentation policy validation end to end. You provide the approved segmentation standard (or a reference snapshot), and the AI agent pulls live segmentation controls, checks them against the intended model, identifies risky deviations, and produces a prioritized remediation list. Instead of periodic audits and spreadsheet comparisons, teams get visibility into whether segmentation rules still reflect the appropriate security model (e.g. least privilege and zero trust intent).
Workflow Steps (Policy Validation & Exception Control)
1. You provide the intended segmentation standard (golden policy or last approved snapshot), including any known exceptions and their rationale.
2. The agent ingests current segmentation controls from all relevant enforcement points (firewalls, cloud security groups, SD-WAN policy sets, micro-seg tools) via API or uploaded files.
3. The agent compares live policy to the intended standard and flags mismatches, such as new allow rules across restricted zones, removed deny rules, broadened CIDR ranges, “any-any” permissions, or redundant/shadowed rules.
4. The agent enriches each flagged item with context by mapping affected assets, applications, and owners using tags, CMDB fields, or ticket metadata. It assigns a risk score based on asset criticality and potential blast radius.
5. The agent outputs a ranked fix plan showing which rules should be reverted or tightened, safer alternatives, and who should own the remediation. High risk findings are posted to Slack or opened as tickets for immediate follow-up.
Value of Automation
Automating segmentation policy integrity checks turns what’s usually a painful, infrequent audit into a regular protection mechanism. Instead of relying on periodic manual reviews, the agent constantly compares live rules to the approved model and flags drift the moment it appears. That means temporary exceptions don’t quietly become permanent backdoors, overly broad rules get caught before they expand blast radius, and shadowed or redundant policies are cleaned up without hours of spreadsheet diffing.
Take Your Next Steps With Kindo
By bringing these network security tasks, from log triage to exposure scanning to configuration auditing, into one intelligent workspace, Kindo helps network security teams move from reactive firefighting to proactive protection.
Routine work like parsing logs, scanning ports, and checking web headers becomes a natural part of a conversation with an AI agent, so your team spends less time on tedious checks and more time on strategic improvements.
If you’re ready to modernize your network security operations, consider exploring Kindo’s AI workflows firsthand. Start with a demo to see how easily these workflows can integrate into your environment.
Interested in additional security content? Check out our previous threat intelligence workflows guide for more on how AI agents can enhance your security operations.




